STOP THREATS
BEFORE THEY ARE EVEN BORN!
DRAGON ENTERPRISE PLATFORM Provides Endpoint Detection and Response Built On Zero Trust Architecture available on our Saas EPP
Our Advanced Auto-Containment System ensures your endpoints are protected against any current or unknown threat in the future.
OUR COMPETITION CANNOT KEEP UP!
Get Started
Xcitium Advanced Endpoint Protection
85 Million Endpoints. 0 Infections!
WE PREVENT CYBERATTACKS & BREACHES THROUGH INNOVATION
Over 850 Cyber-Security Scientists and Engineers bringing Innovation in Cyber Security
Because we understand Science, we understand the Challenges!
There are two Scientific challenges in Endpoint Security today
An undecidable Problem in Computer Science
Alan Turing proved in 1936 that a general algorithm (software code) running on a Turing machine that solves the halting problem for all possible program-input pairs necessarily cannot exist. Hence, the halting problem is undecidable for Turing machines....
What is it?
In computability theory and computational complexity theory, an undecidable problem is a decision problem for which it is known to be impossible to construct a single algorithm that always leads to a correct yes-or-no answer.
Plainly put: A software (algorithm) cannot determine if another software halted or not...
It is not possible to decide algorithmically whether a Turing machine will ever halt.
This theory still holds true today! There is no endpoint security vendor who will claim otherwise...They can't!.
How it applies to Malware detection and endpoint protection?
A malware is an "algorithm" a "software" behavior an antivirus product, whether a legacy antivirus, heuristic based antivirus, behaviour based antivirus, statistics based antivirus or next gen AI based end point protection product is still is "software". And Science has proven it that a "Software" cannot determine if another "Software" halted or not. An Endpoint Protection product has to make a decision about another software and ultimately it has to make this decision without ever knowing if the other software (potentially malicious software) ever finished doing what it is supposed to do or not. Because it can never know that, it can never find all the malicious software. At the end of the day, all these software solutions do nothing but attempt at offering "some" probabilistic solution to the "Halting Problem" which they face, which they know can not be 100%.
Bottom line is, you can never have 100% malware detection using software! Now you have a scientific explanation as to why your endpoint security products let malware in!
There are two security postures for the endpoint security...Default Allow...Default Deny...
Default Allow: Allow everyone in but known bad. Look for bad indicators...allow everyone in who does not have bad indicator
Problem: Halting Problem means you can't detect all bad, which means by allowing everyone you are allowing in potential malware.
Default Deny: Does not detect bad but only allows known good in.
Problem: On its own it is difficult to use, end user experience affected, not practical. In order to mitigate breaches needs to be implemented in a form that is more than a simple application control.
Having a Default Allow posture, while knowing Halting Problem exist (i.e: you can't detect 100% the malware), means you will get infected and suffer a cyber breach. Scientifically proven.
100% Detection does not Exist (Scientifically proven)...You are letting All the Unknowns in!!!!
Problem Summary: Using a "Default Allow" posture
Our Value Proposition for you

- Click on anything
- Run any software
- No more Dwell time
- No more False positives
- No more remediation
- No more chasing tail "trying to detect"

- (World's Only Company to do so)
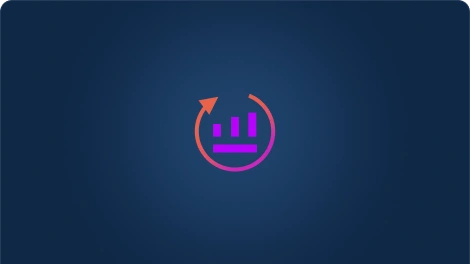
- File exist in 3 states...
- Good, Bad & Unknown
- Allow Good...
- Stop Bad..
- Automatically Contain Unknown
- (in CPU Enforced OS Virtualization)

The Unknown file is the enemy.
We "Temporarily" run the unknown in our patented Containment (CPU-enforced OS Virtualization)

- Once an unknown file is contained...
- We will give each and every file 100% Trusted Verdict!
- We Don't do "Assumption" based verdicts
- We provide SLA for our Verdicts
- We use Human Analysts for 100% trusted verdicts.
- You will KNOW EVERY FILE in your Network!
- You can say: I KNOW there is no Malware in my Network!
The Unknown file is the enemy.
We "Temporarily" run the unknown in our patented Containment (CPU-enforced OS Virtualization)

The Unknown file is the enemy.
We "Temporarily" run the unknown in our patented Containment (CPU-enforced OS Virtualization)

Award Winning Security
to protect your clients from cyber attack
- Click on anything or run any software with no limitation...
- We will make sure everything you run is 100% Safe!
- Heck, go head run live Malware on your computer... You will still be safe!
- With patented OS – Virtualization and Human Intelligence in 100% verdicts overcomes the endpoint security challenges.
- For the first ever, you will achieve Default Deny Security Posture with Default Allow Usability
How We Are Unique
The days of running unknown files are over.... Every file you run will have a 100% Trusted Verdict.
Its time for endpoint security vendors to stop burdening end users with decision and provide verdicts for 100% of each and every file
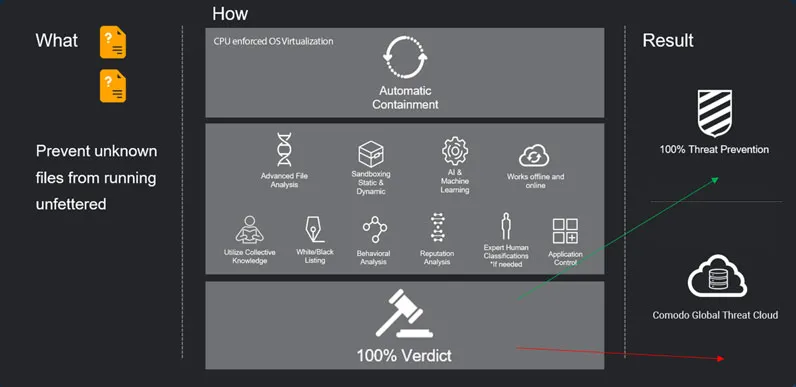
Enhanced Security through shared Intelligence. 13 different capabilities sharing intelligence to make a more informed decision
1 endpoint agent to run....1 endpoint agent to pay for...10 other single point solutions replaced with one Endpoint Security Platform! (3 capabilities ONLY Xcitium offers)
Get Free Trial










