HOW TO PROTECT YOUR NETWORKS FROM RANSOMWARE THREATS
Updated on October 21, 2022, by Xcitium

What Is Ransomware and Why Networks Are Targeted
Ransomware is a type of malware that encrypts data or blocks access to systems, demanding payment for restoration. Attackers target networks because they can spread laterally and impact multiple systems at once, increasing damage and ransom value.
Ransomware targets ordinary users, business users, and even government users. Once it infected a single computer, the next step is to spread the infection all over the local network. Everyone should be informed on how to protect your networks from ransomware threats. This will be helpful in addressing the problem from your PC to the entire network.
When a computer is infected by a ransomware, it too affects the other computers that are connected to the local network. Ransomware is unsafe because once you’re infected, your information can lead to a temporary or permanent misfortune. You’ll be able only regain access once you’ve got paid the demanded ransom of the car proprietor and criminal.
The only way to prevent from being a victim of ransomware is to protect your computer, the network, and all other devices. Threats are expected to increase and no one wants to be a ransomware victim. There must be a strategic plan on how to protect your networks from ransomware threats.
User Training
A regular training regimen is very helpful if you want to know how to protect your networks from ransomware. Every user must be informed about the methods of the cybercriminals on how they conduct their attacks. The user must be familiar with the social engineering techniques of the criminals.
Software Update of Server and Workstations
It is vital that all the server and workstations must always be updated. It means that all the latest patches released by the legitimate source must be installed. Most of the small businesses do not update. The attackers take advantage of this and make them the primary target.
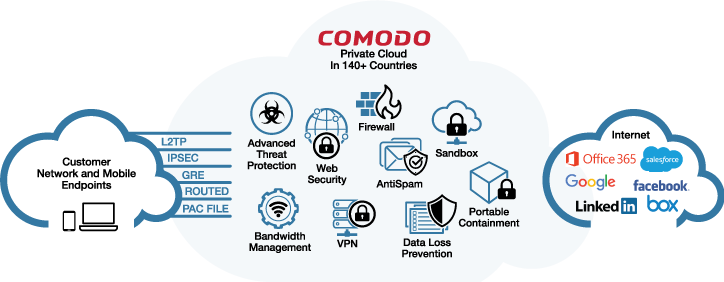
Security Software
Having a security software is another way how to protect your networks from ransomware. This security software has the capacity to scan and trace any malicious behavior. Just beware of the different kinds of security software because some of the signature-based security software could not detect the ransomware. Security software will also protect your computer when you are browsing the internet. This will prevent malware from entering your computer via website visit. If all servers, workstations and all other devices are properly secured, it would not be difficult to secure the whole network.
Regular Backup
The most common method on how to protect your networks from ransomware is by having a backup. Although this is the most common, many small-sized businesses failed to perform this. When the time they are attacked by the ransomware, their option is to pay the ransom just to retrieve important documents. This backup should also be tested regularly.
Vulnerability Checks
Assessing vulnerabilities in every network is beneficial in executing on how to protect your Networks from ransomware. The person to analyze the network must be knowledgeable about how the ransomware conducts its attacks. This could be done on a yearly basis.
Regular Monitoring
Performing regular monitoring of the whole network is a great advantage on how to protect your networks ransomware. Through the monitoring, all the suspicious activity are traced. In this way ran attack are prevented. There must also be a dedicated person just to the now next step.
How To Protect Your Networks From Ransomware Threats: What To Do If Infected
If the, by all means, the prevention fails and you don’t know how to protect your networks from ransomware threats, there are steps on how to mitigate the infection in the network.
- Isolate the Infected Computer
When the presence of a ransomware has been identified in a computer, it must be isolated to the network immediately to avoid the spreading of the infection to the whole network. - Immediately Secure a Copy of a Clean Backup
A clean copy of backup that is free from any strains of ransomware must be immediately secured. - Change all Security Accounts
If a ransomware has been detected on the network. It is better to immediately change the passwords because old passwords might already be compromised. - Delete Registry Values
If you are capable, delete all the registry values and files to stop the program from loading. - Contact Law Enforcement
It is better to report the incident to your law enforcement unit in case of a ransomware attack.
By having a plan on how to protect your networks from ransomware will save you a lot of money and time. Ransomware threats are always there looking for a weak point. If you fail to plan, criminals will likely lead to lost business customers and decreased revenue.
How to Protect Your Networks from Ransomware (Step-by-step)
- Implement regular data backups
- Store backups offline or in secure cloud environments.
- Keep systems and software updated
- Patch vulnerabilities to prevent exploitation.
- Use advanced endpoint protection
- Deploy antivirus and EDR tools for real-time threat detection.
- Enable multi-factor authentication (MFA)
- Protect user accounts from unauthorized access.
- Segment your network
- Limit ransomware spread by isolating critical systems.
- Monitor network traffic continuously
- Detect suspicious activity using IDS/IPS solutions.
- Restrict user permissions
- Apply least privilege access to reduce risk.
- Train employees on cybersecurity awareness
- Prevent phishing and social engineering attacks.
How Ransomware Spreads Across Networks
Common Attack Vectors
| Attack Method | Description |
|---|---|
| Phishing emails | Malicious attachments or links |
| RDP attacks | Unauthorized remote access |
| Exploits | Unpatched vulnerabilities |
| Drive-by downloads | Infected websites |
Network-Level Security Measures (CRITICAL SECTION)
1. Network Segmentation
- Divide networks into smaller zones
- Prevent lateral movement of ransomware
2. Firewalls & Intrusion Detection Systems
- Block malicious traffic
- Detect suspicious behavior
3. Zero Trust Architecture
- Verify every user and device
- No implicit trust within the network
4. Secure Remote Access
- Use VPNs and MFA
- Disable unnecessary RDP access
Endpoint vs Network Protection
| Feature | Endpoint Security | Network Security |
|---|---|---|
| Focus | Individual devices | Entire network |
| Threat detection | Malware & files | Traffic & behavior |
| Protection scope | Limited | Broad |
| Best use | Device-level defense | Prevent spread |
Best Practices for Enterprise Ransomware Protection
- Maintain offline backups
- Use AI-based threat detection
- Monitor real-time network activity
- Conduct regular security audits
- Implement incident response plans
What to Do If Ransomware Hits Your Network
- Isolate affected systems immediately
- Disconnect from the network
- Identify the ransomware strain
- Use removal tools
- Restore from backups
- Conduct forensic analysis
FAQ
How do you protect a network from ransomware?
You can protect a network from ransomware by using backups, patching systems, enabling MFA, monitoring network traffic, and implementing segmentation and endpoint security.
Can ransomware spread across networks?
Yes, ransomware can spread laterally across networks, especially if systems are not segmented or properly secured.
What is the best defense against ransomware?
The best defense is a layered approach that includes endpoint protection, network monitoring, backups, and user awareness training.
How do companies prevent ransomware attacks?
Companies prevent ransomware by using advanced security tools, enforcing access controls, and continuously monitoring systems for suspicious activity.
Protect Your Network with Xcitium
- Zero-day ransomware protection
- Automated threat containment
- Real-time network monitoring
- Advanced forensic analysis
👉 Built to secure your entire network from modern ransomware threats
Related Sources:
Trojan Virus
Ransomware Software