What are the Best Malicious Malware Removal Methods?
Updated on October 21, 2022, by Xcitium
Once malware infects your computer, it attacks the file system and targets valuable files. Before it does further damage on the computer, you must get rid of malware by performing some effective malicious malware removal methods.

3 Malicious Malware Removal Methods
1. Method No. 1 - Safe Mode
Windows only launches minimum programs in Safe Mode. This prevents malware from running and damaging the computer any further.
- Enter Safe Mode
- Once the computer boots up in Safe Mode, type MSCONFIG in the search bar
- On the dialogue box, click on the Startup tab
- Check out if there’s any suspicious file in the list of applications(Check for the program and publisher on the Internet.)
- Disable the suspicious application
- Click Apply then Ok
- Exit but don’t restart the computer yet
That should prevent malicious malware from running on the computer.
Method No. 2 - Clear Temporary Files
When malware enters the computer, it usually hides in the TEMP folder. It mixes up with the legitimate exe files in the TEMP folder. The security in the TEMP folder is normally low, so malware can lurk there.
- To go to the TEMP folder, type %temp% in the Windows search bar
- When the TEMP folder, you’ll see a bunch of temporary files. Delete all.
- Close the folder
With the temporary files deleted, your computer is partially free of malware.
Method No. 3 - Malware Scanning
Even if you have successfully disabled malware and cleared the temporary files, there’s a chance that stubborn malware remains in the computer. To ensure a complete malicious malware removal, let’s scan the computer with a malware scanner. If you don’t have a malware scanner yet, look for a free malware scanner such as Xcitium Anti Malware. It is a good malware removal tool for a personal computer.
- Click here to download Xcitium Anti Malware
- Once downloaded and installed, open the user interface
- Click on Scan
Xcitium Anti Malware will scan the entire computer for malware and remove it. That completes the malware scanning and removal process.
How to Scan the Endpoint Devices for Malware?
In an organization, scanning endpoint devices is essential. A vulnerable endpoint device can be the point of section of malware. Malware can spread within the network. So it is vital to keep the endpoint devices secure by scanning them.
Scanning endpoint devices can be accomplished through a malware removal tool with endpoint protection. The security software only needs to be installed on the central server then the anti malware software can scan the endpoint devices for malware.
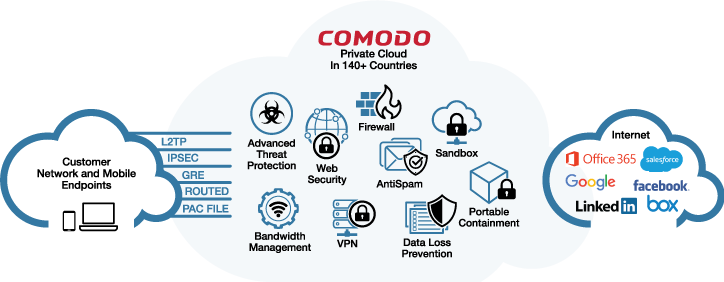
Xcitium Advanced Endpoint Protection is a reputable security solution for an enterprise. It is trusted by 600,000 companies and protects 85 million endpoint devices worldwide.
Notable Features of Xcitium Advanced Endpoint Protection
Auto-Containment
The Auto-Containment is a good malicious malware removal tool. It has a Default Deny feature that prevents untrusted software from accessing the file system. When a suspicious file enters the computer, it is automatically contained. The Auto-Containment prevents:
Spear Phishing Attacks
Drive-by-Download Infections
Ransomware Attacks
Zero-Day Exploits
Host Intrusion Prevention System
The Host Interruption Prevention System monitors the computer memory and registry against fileless malware. When fileless malware attempts to get to the computer memory, the Host Intrusion Prevention System immediately detects it. It also protects the computer against sophisticated malware that evades the detection of the antivirus and firewall.
VirusScope
VirusScope is an advanced machine learning technology. It consists of multiple recognizers that detect sophisticated malware in no time. It is fed with various good and bad software to make it an effective malicious malware removal tool. So when a file enters the computer, VirusScope can easily determine if it’s malicious or safe.
Firewall
The firewall protects the network and endpoint devices by:
Filtering network traffic
Monitoring data transmission
Monitoring the active applications on endpoint devices
The firewall can also prevent spear phishing attacks.
Cloud-Based Antivirus
The Antivirus is a powerful defense against known threats such as trojan, spyware, adware, rootkit, worms, and viruses. It is a cloud-based malware removal tool, which means that even if the security software is not updated, it can still protect the computer against the latest threats.
Valkyrie
Is a cloud-based platform that uses static and dynamic analysis to detect threats. It can determine if a file is safe or harmful in just 40 seconds. If there’s not enough information about the file, Valkyrie sends the data to a human expert for analysis.
A business network with a multi-layered defense will not fall victim to cyber attacks. Even if malware attacks are increasing, your valuable files are secured. Download Xcitium Advanced Endpoint Protection today or contact us for a live demo.
Free Malware Discovery Get Free Trial
Related Sources:
What is Trojan Horse? Lock Screen Ransomware