Lock Screen Ransomware Removal Using Xcitium AEP
Updated on October 21, 2022, by Xcitium
How Lock Screen Ransomware Works
Lock screen ransomware infects a device through phishing emails, malicious downloads, exploit kits, or compromised websites. Once installed, the malware displays a full-screen ransom message that blocks access to the desktop and prevents users from using the system normally.
Most lock screen ransomware variants:
- Infect the endpoint
- Modify startup settings
- Disable system controls
- Display a fake law enforcement or payment warning
- Demand ransom payment to restore access
Advanced variants may also disable:
- Task Manager
- Safe Mode
- Security software
- System restore features
It’s just another day on the Internet, until you come onto a site which asks you to confirm something but then all of a sudden your screen seizes and you see a message from a lock screen ransomware. The ransomware says Homeland Security knows you’ve browsed an illegal site and now you have to pay. Your operating system is completely locked out by the ransomware and you feel you have no options but to pay.
An encounter with lock screen ransomware can be an unsettling experience. Since this particular ransomware will frighten you and then extort money from you as it locks you away from your computer. Is there a solution for this particular ransomware?
Common Examples of Lock Screen Ransomware
Several ransomware families have used lock screen tactics to extort victims.
Reveton
Reveton displayed fake law enforcement warnings claiming illegal activity was detected on the victim’s device and demanded payment through prepaid vouchers.
WinLock
WinLock blocked desktop access and required victims to send premium SMS payments to unlock systems.
Police-Themed Ransomware
These variants impersonated government agencies and accused users of illegal online activity to pressure victims into paying fines.
Including ransomware examples improves semantic relevance and E-E-A-T signals.
How to Remove Lock Screen Ransomware
To remove lock screen ransomware safely:
- Disconnect the infected device from the network
- Boot into Safe Mode if accessible
- Run advanced anti-ransomware software
- Remove malicious startup entries
- Restore system settings
- Scan for additional malware infections
- Restore clean backups if necessary
Organizations should avoid paying ransom demands because payment does not guarantee system recovery.
How to Prevent Lock Screen Ransomware
Organizations can reduce ransomware risk by implementing layered endpoint protection and cybersecurity best practices.
Recommended Prevention Measures
- Use advanced endpoint security software
- Enable behavioral ransomware detection
- Regularly update operating systems
- Restrict unauthorized applications
- Train employees to recognize phishing emails
- Maintain offline backups
- Use zero trust security policies
- Monitor endpoint activity continuously
Signs of a Lock Screen Ransomware Infection
Common symptoms include:
- Full-screen ransom messages
- Inability to access the desktop
- Disabled keyboard shortcuts
- Restricted Task Manager access
- Fake law enforcement warnings
- Unexpected payment requests
- System startup lockouts
Recognizing these symptoms early can help contain ransomware before it spreads.
AEP Protects Your Computer from Lock Screen Ransomware
Lock screen ransomware have been making a comeback after ransomware authors stopped using this form of malicious software for some time. The last spate of widespread inspection of lock screen ransomware occurred in 2015 until gaining resurgence in 2017. Considering that a lock screen ransomware locks away your operating system instead of just a few choice files like most ransomware do makes lock screen ransomware much more troublesome. The reemergence of this type of ransomware is not welcome news.
How A Computer Lock Screen Ransomware Works
In order to understand how this type of Ransomware takes root, one has to see how it gets delivered onto a computer. The key delivery method so far is through malicious, infected sites. Lock screen ransomware ride along fake advertisements seen in malicious websites. Sometimes readers end up going a questionable website to read articles there. They encounter a pop-up ad which warns them that their computer has been infected and they download a file. When they click it, the malicious website downloads the lock screen ransomware onto their computer. The lock screen ransomware then proceeds the operating system.
By playing with a user’s fear, ransomware authors are able to manipulate them into infecting their computers with ransomware. This is an example of social engineering or manipulating a person in order to capitulate with a person’s wishes into performing a particular task which, in this case, is to confirm a command that downloads lock screen ransomware onto the device. A prompt appears announcing that hackers hold the contents of the drive in hostage and will only decrypt it if the victim pays a sum. Since we live in an age where digital information is an important resource, the victim complies with the extortion.
Imagine what kind of chaos lock screen ransomware can do to an institution like a bank?
The threat of ransomware becomes more and more serious considering the explosion of incidents in recent years. Aside from malicious websites and false advertisements, there is a recorded growth of ransomware delivered through phishing emails from 92% to 97.25% in 2016 alone. A study conducted by a team of researchers from Friedrich-Alexander University in Germany shows that 78% of email users are aware of the threat of unknown links to email security and yet they click them anyway.
Obviously, ransomware is not a threat any group should take sitting down. An anti-malware and lock screen ransomware solution is in order.
AEP Vs. Lock Screen Ransomware
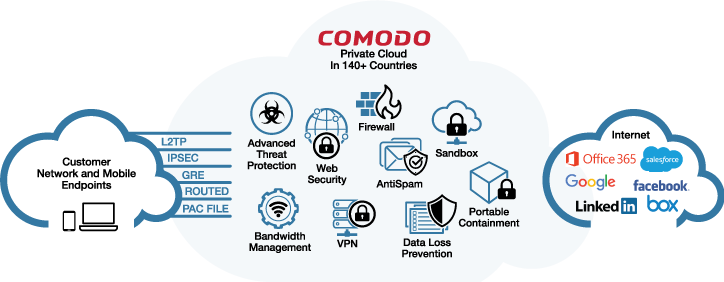
Fortunately, there’s Xcitium’s AEP or Advanced Endpoint Protection software to counter the very threat of lock screen ransomware. The AEP is an anti-malware solution for individuals and organizations geared towards protecting them from ransomware.
Xcitium engineered AEP on a Default Deny Platform which allows good files to run while simultaneously blocking bad files. The AEP runs unknown files in a safe environment isolated away from the rest of the files on the computer drive while Valkyrie, a program which judges if the processes from a file resemble those of malware or lock screen ransomware, scans and decide on the event. As you can see, AEP can safely lock away ransomware by allowing it to run in a controlled environment and remove it when shows its harmful side.
Aside from this, Xcitium Advanced Endpoint Protection offers the following distinct advantages against ransomware:
- 1. Cloud-based management
- 2. Controls Android, iOS, and Windows devices under one console
- 3. Controls devices, apps, and security in one interface
- 4. Remote installation and anti-theft features like find-my-phone and sneak-peek
- 5. Automatically contains files and analyzes them for malware or ransomware
- 6. Combination of software and human analysis of files to check for threats
- 7. Remote monitoring and management of files with option to control device from a distance
- 8. Ability to apply patches securely
- 9. Transparent listing of all running computer processes or file processes
- 10. On-demand scanning for malware or ransomware
- 11. Plus firewall, web URL filtering against malicious websites with ransomware, jailing protection, whitelisting, and VPN
AEP Crushes Lock Screen Ransomware Before It Even Starts
Considering the damage that a lock screen ransomware can wreak on your system, the best form of action is to be proactive and lock down any opportunity that one will download onto your computer. This means you must avoid going to questionable sites and using an advanced scanner like Xcitium Advanced Endpoint Protection to shut down lock screen ransomware before it even begins to infect your system.
In this regard, when you or your organization needs protection from ransomware and malware, you can rely on Xcitium Advanced Endpoint Protection to shield your computers. Since the software scans processes and triggers files in a contained space, it is also effective in catching zero-day threats like the newest strains of ransomware.
Aside from a comprehensive ransomware and malware protection package, AEP will save you from worry and save you time and money you’ll use to recover in case your computers got infected by lock screen ransomware. You can avail of a 30-day free trial period to see how effective AEP is in protecting you from threats and can then subscribe for a measly $4 per computer per month. This is a small sum to pay compared to the anxiety and the amount hackers are charging to decrypt your operating system from their lock screen ransomware creations.
Download your free trial of Xcitium Advanced Endpoint Protection now.
Frequently Asked Questions
What is lock screen ransomware?
Lock screen ransomware is malware that blocks access to a device by displaying a full-screen message demanding payment. Unlike crypto ransomware, it typically does not encrypt files.
Can lock screen ransomware encrypt files?
Most lock screen ransomware variants focus on denying device access rather than encrypting files. However, some modern ransomware families combine both techniques.
How does lock screen ransomware spread?
Lock screen ransomware commonly spreads through:
- Phishing emails
- Malicious downloads
- Fake software updates
- Exploit kits
- Compromised websites
Can antivirus software stop lock screen ransomware?
Advanced antivirus and endpoint protection platforms can detect and block ransomware behavior using behavioral analysis, real-time monitoring, and threat intelligence.
Should victims pay the ransom?
Cybersecurity experts and law enforcement agencies generally advise against paying ransom demands because payment does not guarantee recovery and may encourage further attacks. Try it for FREE