UNDERSTANDING WHAT IS A KEYSTROKE TRACKING SOFTWARE
Updated on October 21, 2022, by Xcitium
A keystroke tracking software is an application that can intercept and record keystrokes, making it a potential tool for getting a hold of personal information.
![]()
However, most of us are unaware that keystroke tracking software has beneficial uses too. In this article, we will highlight the different uses of keyloggers, how it works for personal and business use, and as malicious software.
USES OF KEYSTROKE TRACKING SOFTWARE
Personal Use
Keystroke tracking software can be used by people who want to monitor their family members. Parents, for example, can use keystroke tracking software to monitor their children’s online activities. They can install keylogging software on their children’s mobile devices. This gives them access to their children’s online searches, SMS, and call logs.
Suspicious spouses can also use a keylogger to confirm their suspicions. They can install a keystroke tracking software on their partners’ smartphones to see who they are talking to. Using a keystroke tracking software they can read their partners’ personal conversations.
Business Use
Keystroke tracking software is also deployed in the workplace. Some companies install keylogging software on work computers to monitor employees’ activities. By being able to read what employees type on their device, they can track employees’ activities.
This is legal. Employees are also aware that employers install keystroke tracking software on their devices for business purposes. Employers should be able to see employees’ online searches, emails, and more.
Malicious Software
Using a keylogging software maliciously is what makes it a serious threat. Keystroke tracking software can record the exact characters typed on the keyboard. Hackers take advantage of this and use keystroke tracking software to steal personal information.
They spread keyloggers using different methods to steal username, passwords, and confidential data from consumers and companies. Using the stolen information, they can log into personal accounts and make unauthorized transactions.
Unfortunately, keystroke tracking software is commonly use for stealing personal information and credentials. So you have to protect yourself from a keylogging attack.
WHAT ARE THE WAYS TO PROTECT YOURSELF FROM Keystroke Tracking Software?
Use 2-Step Verification
Using a 2-Step verification is an effective way to avoid falling victim to a keylogging attack. It sends a pin code to your mobile number and requires you to enter it before you are able to log into your account. Even the hacker obtains your username and password, he still has to enter the pin code before he gains access to your account.
Use Key Encryption Software
Key encryption software is also a great tool for concealing the characters you type on the keyboard. It encrypts the keys as they travel through the operating system, preventing keystroke tracking software from capturing the exact characters you enter.
Copy-Paste
Copying and pasting sensitive information is a technique to prevent keystroke tracking software from monitoring your personal information. Since you don’t have to enter the information through the keyboard, the keystroke tracking software won’t be able to log it.
Voice Recognition
You can also use voice recognition when you are logging into your account to prevent keystroke tracking software from stealing your personal information. Using voice recognition you don’t have to type your username and password to access your account.
Install Anti Malware Software
Anti-malware software protects your computer from keystroke tracking software and other types of malware. It scans files and file systems regularly to detect hidden threats on the computer. Installing anti-malware software is a sure way to protect yourself from keystroke logging attacks.
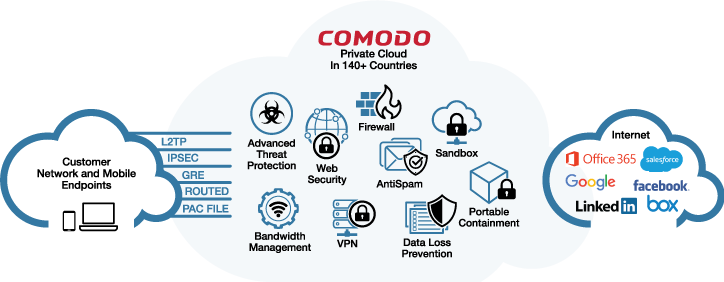
Keystroke Tracking Software: Xcitium ADVANCED ENDPOINT PROTECTION
Xcitium Advanced Endpoint Protection is an anti-malware software that is ideal for small to medium enterprises. It is designed specifically to protect a business network and endpoint devices. It prevents malware infections.
Hard Drive Protection
Xcitium Advanced Endpoint Protection protects sensitive information and files on endpoint devices by monitoring the hard drive against direct access. It verifies if the file is safe before it is given access to the file system.
Keyboard Monitoring
Xcitium Advanced Endpoint Protection also prevents a keystroke tracking software from intercepting keystrokes by constantly monitoring the keyboard. It verifies the reputation of the application which attempts to access the keyboard.
Computer Memory and Registry Monitoring
Xcitium Advanced Endpoint Protection also monitors computer memory and registry against malicious modifications. Using a unique feature, Xcitium AEP prevents registry keys from unauthorized modifications to ensure that only legitimate applications load in Startup.
Keystroke-tracking software can be used to steal personal information from consumers and companies. So it is important to protect your computer with reputable anti-malware software.
Download Xcitium Advanced Endpoint Protection today to protect your endpoint devices from a keylogger attack. Or contact us to get a live demo.
Related Sources: