Ransom Computer Virus
Ransom Computer Virus is a malware that you will not want to hit your computer. It is one of the major cyber threats today. It’s been attacking personal computers and company networks. We keep hearing ransomware attack hospitals, banks, newspaper companies and more on the news. Large corporations’ operations have been seriously affected.
 Ransom computer virus attack guarantees the loss of sensitive and valuable information without an assurance of recovering files unless the files have been backed up. Paying the ransom doesn’t always guarantee files recovery. So cybersecurity experts don’t recommend paying up the ransom and advise the users to have a cloud-based backup.
Ransom computer virus attack guarantees the loss of sensitive and valuable information without an assurance of recovering files unless the files have been backed up. Paying the ransom doesn’t always guarantee files recovery. So cybersecurity experts don’t recommend paying up the ransom and advise the users to have a cloud-based backup.
What is the best way to combat Ransom Computer Virus
Ransom computer virus attacks the computer or network without a warning. It is just looking for a vulnerability to exploit. Once it finds a system vulnerability, it infiltrates the system. This is covert so that users are unaware that ransom computer virus is already encrypting the files.
Before, ransom computer virus required an execution to encrypt files. Now, it has grown more sophisticated; it directly attacks the computer memory. Instead of writing its script on the computer disc, it writes its script directly into the computer RAM to avoid detection when the anti-malware scans the hard drive.
This means that it can modify the registry at its will. Since this ransom computer virus leaves no trace of its installation, it’s more dangerous and destructive. Traditional anti malware software cannot detect this type of ransom computer virus.
This is the new age cyberattack. It is more stealthy and advanced. No one is exempted from ransom computer virus attack. Everyone is vulnerable since many rely on the Internet to accomplish a task. We use an email and visit different websites almost every day. That’s how ransom computer virus often enters the computer and network.
So taking preventive measures is a must today. We don’t want to get hit by ransom computer virus because not only it’s a hassle, it also frustrating. You lose your files and money at the same time. Since ransom computer virus is more sophisticated now, it may go undetected using traditional anti-malware software.
What is the best way to protect the computer and network?
What is Endpoint Ransom Protection
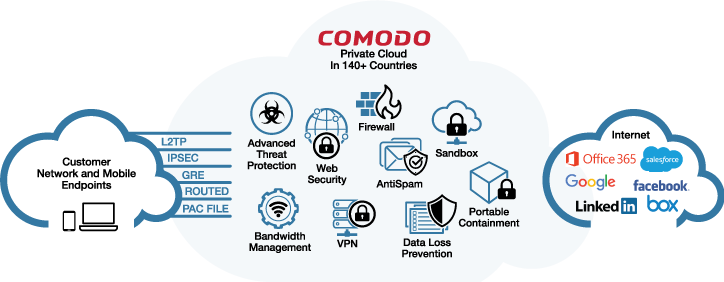
Endpoint Protection is a central approach that is used to protect a large network such as a corporate network by securing the endpoint devices. Many network owners allow access to endpoint devices like laptops, mobile devices, tablets, and more. Do you know that these endpoint devices can be the entry point of a ransom computer virus?
A simple phishing email can infect endpoint devices then it can spread through the network. So it is important to secure the endpoint devices. Also, endpoint devices are one of the targets of cybercriminals today.
They’re aware that these endpoint devices have access to a large or business network. By infiltrating the endpoint device, they can also hack the entire network. What if a ransom computer virus attacks any of your devices today, is your network secure?
Xcitium Advanced Endpoint Protection
Xcitium being aware of these endpoint devices vulnerabilities, developed a central security software to protect the endpoint devices. This endpoint protection software is installed on the main server that monitors endpoint logins and activities.
It has Remote Monitoring Management (RMM) that enables remote installation on the endpoint devices, so the endpoint protection software can be installed on multiple devices from the admin computer.
If you have Xcitium Advanced Endpoint Protection you need not worry about your endpoint devices. It is equipped with the essential tools to combat malware such as ransom computer virus.
In the recent 2018 Cybersecurity Excellence Award, Xcitium Advanced Endpoint Protection named the best Ransomware Protection specifically for its Auto-Containment Technology. It’s a feature that protects the endpoint devices from untrusted and unknown files by denying their execution on the computer unless they have been closely analyzed.
Auto-Containment runs the file within a protected container to observe its behavior. To monitor how it behaves, Auto-Containment replicates the hard drive so it tricks that file that has complete access to the computer, but that is just one strategy to evaluate its behavioral pattern.
Another feature of Xcitium Advanced Endpoint that fights against fileless ransomware is HIPS or Host Intrusion Prevention System. It is designed to monitor the registry and computer memory against modification.
Conclusion Ransom Computer Virus
So if fileless malware attempts to write its script into the computer RAM, HIP will instantly detect and block it. It also guards the keyboard and other devices to ensure that no malware is stealthily tracking and recording the keystroke to protect the passwords.
Xcitium Advanced Endpoint Protection also has a pocket filtering firewall that filters the network traffic to prevent suspicious data transmission and malicious activities. Xcitium Firewall protects the endpoint devices by monitoring the active applications that send and receive data.
It is one of the best security software that you can have for your endpoint devices and networks. Xcitium Advanced Endpoint Protection never leaves a window for a ransom computer virus to infiltrate the endpoint devices and network.
Download Xcitium Advanced Endpoint Protection now for free.