How people get ransomware (and what to do about it)
Updated on October 21, 2022, by Xcitium

How do people get ransomware?
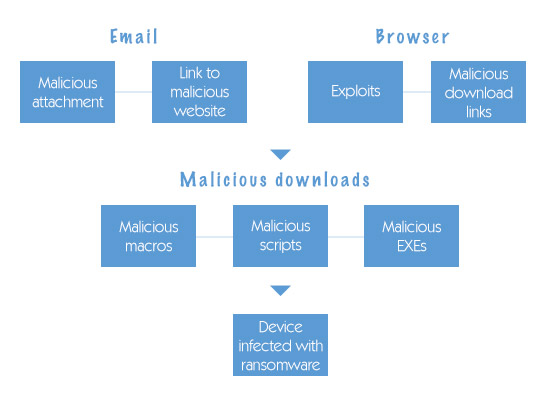
People get ransomware mainly through phishing emails, malicious downloads, unsafe websites, and unpatched software vulnerabilities. Attackers trick users into clicking links or opening infected files, which installs ransomware and locks their data.
At present, the only way people get ransomware is for them to be tricked into downloading and activating it. In principle, this means that you could avoid being attacked by ransomware just by being very careful about what you did online and how you treated your emails. In practice, while this is certainly strongly recommended, there is now so much ransomware that you need to take a more strategic approach and use software tools to help. With that in mind, here’s a quick guide on how people get ransomware (and what to do about it).
8 Common Ways People Get Ransomware
- Phishing emails (most common)
Fake emails with malicious links or attachments trick users into installing ransomware. - Malicious attachments and links
Files like PDFs, ZIPs, or Word docs can carry hidden ransomware payloads. - Visiting compromised websites (drive-by downloads)
Simply visiting an infected website can trigger automatic malware downloads. - Downloading pirated or untrusted software
Cracked apps often contain hidden ransomware. - Unpatched software vulnerabilities
Outdated systems allow attackers to exploit security flaws. - Remote Desktop Protocol (RDP) attacks
Weak or exposed remote access systems are easy entry points. - Malvertising (malicious ads)
Clicking infected online ads can silently install ransomware. - Infected USB drives or external devices
Malware can spread through removable media.
How ransomware spreads
| Infection Method | How It Works |
|---|---|
| Phishing emails | Tricks users into clicking malicious links or attachments |
| Drive-by downloads | Malware installs when visiting infected websites |
| Software vulnerabilities | Hackers exploit outdated systems |
| Pirated software | Hidden malware bundled with downloads |
| RDP attacks | Attackers access systems remotely |
| Malvertising | Malicious ads install ransomware |
| USB devices | Infected external devices spread malware |
Email attachments
Automated email filters have done a lot to block the sort of spam emails that were once notorious for spreading malware. The problem is that these filters are of limited use in targeted social-engineering attacks. That’s why the only safe option is to insist that all email attachments are scanned by a reputable anti-malware program before they are opened, even if they appear to come from a trusted source. If this seems harsh, then remember that even a legitimate trusted source can make a mistake or have their account compromised (or spoofed).
USB ports
Although it’s relatively unusual for malware to be spread through hardware, it does happen and it’s particularly likely to happen for ransomware because the potential pay-off makes it worth the effort. Securing desktops (and desk-based laptops) is fairly straightforward. The key point is to stop people using USB ports and optical drives as a backdoor to installing software. Protecting mobile devices can be rather more complicated.
With mobile devices, you need to think about protecting the operating system and apps (with a reputable anti-malware program), plus making sure they connect to the internet safely (via secure WiFi or mobile data, possibly coupled with a VPN) and protecting the hardware itself. In practical terms, this means eliminating (or at least reducing) the extent to which the device is connected to third-party hardware, such as charging stations. So, for example, you’d look to provide your staff with power banks they could use instead.
Social media
While it has to be said that most social-media use is at worst harmless and at best can be very beneficial, the popularity of social media, especially the major platforms, makes it a huge draw for malicious actors. From the perspective of getting ransomware, possibly the single, biggest potential trap is short links.
In principle, it’s easy enough to check where a short link goes. In practice, most people who use social media for fun (rather than for work) are in relaxed mode and not as security-conscious as they should be. That’s why social media platforms are such tempting draws for cybercriminals.
Given that most people now have smartphones and may have tablets as well, you may want to consider the possibility of just restricting the company internet connection for company business. You could soften the blow by setting up a “social” WiFi network and/or allowing people to charge their phones at work. If this is a step too far, then you absolutely must make sure that you have a robust anti-malware program with an integrated firewall.
Malvertising
Malvertising is the practice of buying advertising space and then using the adverts to spread malware. Most malvertising relies on the user being tempted to click on the advert, but sometimes it’s enough for the advert to be displayed on the screen. The easiest way to put a stop to this is to use an ad blocker and these are often included with security software. That said, some websites may insist that you allow adverts to access them. If you consider them worth it, then you’ll need to rely on a reputable anti-malware program with a firewall.
Automatic downloads
Never allow automatic downloads. It’s literally just asking for trouble.
Protecting yourself against ransomware attacks
As you will probably have gathered from this article, your key defense against ransomware attacks is a reputable anti-malware program with an integrated firewall. It is extremely risky to rely on the default security programs bundled with the main operating systems.
You also need to ensure that all the operating systems and locally-installed apps you use are promptly updated. For completeness, cloud-based apps will be updated by the vendor. It is crucial to apply updates as quickly as possible so if you know this is an issue in your organization, then it’s advisable to have a managed IT services provider do it for you.
Additionally, you need to ensure that all sensitive data is stored encrypted and that you have an off-site database which is entirely separate from your main system. This means that if you do fall victim to encryption ransomware, your data will be safe from theft and you can just restore from your backup.
FAQ
What is the most common way people get ransomware?
Phishing emails are the most common method, where attackers trick users into clicking malicious links or opening infected attachments.
Can you get ransomware just by visiting a website?
Yes, through “drive-by downloads,” where malware installs automatically from compromised websites.
How fast can ransomware infect a computer?
Ransomware can start encrypting files within minutes after execution, depending on the variant.
Who is most at risk of ransomware attacks?
Individuals and organizations with outdated software, weak security, or poor user awareness are most vulnerable.
Please click here now to start your free 30-day trial of Xcitium AEP.