how does
Updated on October 21, 2022, by Xcitium
Updated on October 21, 2022, by Xcitium
Please give us a star rating based on your experience.
Anti Malware: Malware Protection Malware protection is often mistaken as a simple security against m...

Malware Virus is defined as a harmful application that pretends to be useful software. Malware virus...

Computer malware protection is a multi-layered defense against varieties of malware. It is an essent...
Malware can hit a PC without a good computer malware cleaner. But before cleaning the computer for v...

Ransomware is a specific type of computer malware that encrypts a victim’s files or systems to...
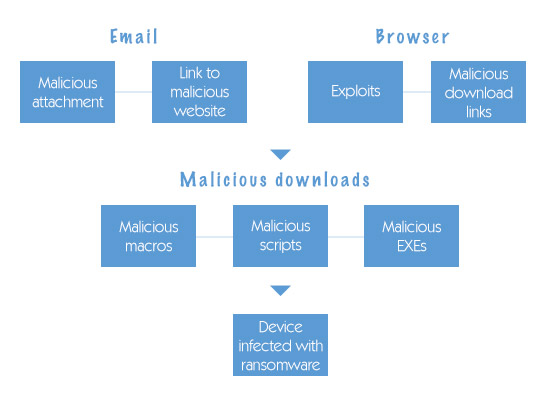
How Does Ransomware Get on your Computer? Ransomware is an advanced form of malicious malware that h...
Malware finds its way to the computer with one primary objective; stay hidden until the goal ...
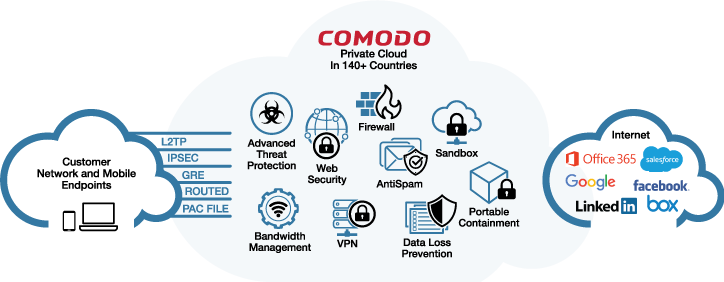
Cloud-Delivered Secure Web Platform Xcitium Dome is a revolutionary Cloud Delivered Secure Web Platf...

Deal With Ransomware On Linux: Ransomware on Linux For years Ransomware on Linux, and its close rela...
Ransomware attacks are rampant nowadays. It is no wonder because different social engineering techni...
Scan Computer Online To Protect Your PC When a computer is infected with a virus, there are a lot of...
Definition of Computer Malware: Computer Malware Cyber criminals designed computer programs to penet...