security solutions
Updated on October 21, 2022, by Xcitium
Updated on October 21, 2022, by Xcitium
Please give us a star rating based on your experience.
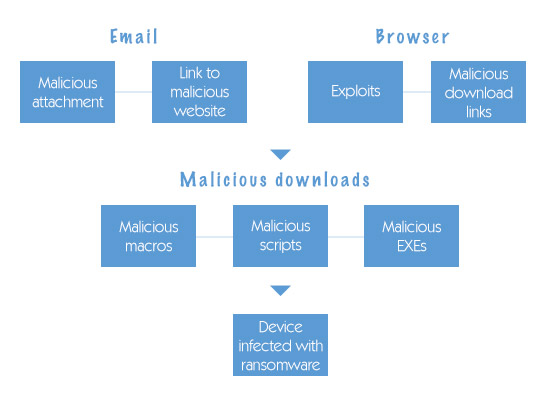
How Does Ransomware Get on your Computer? Ransomware is an advanced form of malicious malware that h...

Organizations are at the verge of security risks or data breaches leading to high amounts of data lo...
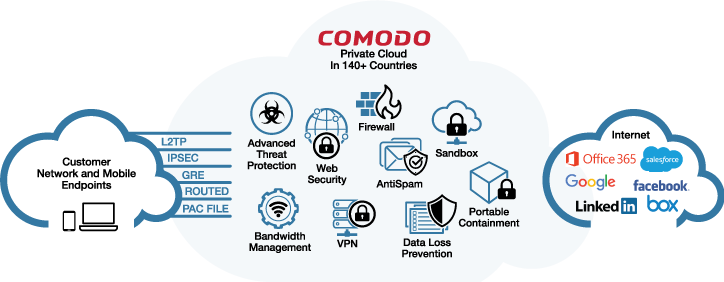
Cloud-Delivered Secure Web Platform Xcitium Dome is a revolutionary Cloud Delivered Secure Web Platf...
Xcitium Email Security Certificates Electronic communication is fast and efficient, but increasingly...
Numerous ransomware attacks occur worldwide. But there are certain ransomware attacks that stand out...
Malware Virus is defined as a harmful application that pretends to be useful software. Malware virus...
Malware can hit a PC without a good computer malware cleaner. But before cleaning the computer for v...

You’ll know if you have ransomware because it will send you a message to tell you. What you need t...
Malware is stealthy and can get installed on your computer without your permission. It finds its way...
A computer malware attack may render your PC and files useless. It also compromises your personal in...
Once malware infects your computer, it attacks the file system and targets valuable files. Before it...
Ransomware Examples Xcitium AEP’s Rendered Useless Xcitium has been fighting different types of ra...