How to remove the ransomware virus
Updated on October 21, 2022, by Xcitium

How do you remove the ransomware virus?
To remove a ransomware virus, you must immediately isolate the infected device, eliminate the malware using security tools, and restore data from backups or decryption tools. Quick action is critical to stop the ransomware from spreading and causing further damage.
Ransomware is already a wide-scale threat and new forms of it are being created all the time. Although you should always try to avoid getting it in the first place, sometimes you just have to deal with it. With that in mind, here is a guide on how to remove the ransomware virus.
What to do immediately after a ransomware attack
- Disconnect the infected device from the internet
- Disable Wi-Fi, LAN, and cloud sync
- Remove external drives and backups
- Stop access to shared networks
- Inform IT/security teams immediately
➡ Isolation prevents ransomware from spreading across systems and networks
Step-by-Step: Remove the Ransomware Virus
Step 1: Isolate the infected system
Disconnect all network connections to prevent lateral movement.
Step 2: Boot in Safe Mode
Restart the system in safe mode to stop ransomware processes from running.
Step 3: Identify the ransomware strain
Use ransomware identification tools to determine the variant and available decryption options.
Step 4: Remove malware using security tools
Run advanced anti-malware or endpoint detection tools to:
- Scan the system
- Quarantine threats
- Delete malicious files
Step 5: Wipe and reinstall (if needed)
For severe infections:
- Perform a full system reset
- Reinstall the operating system
- Apply all security updates
➡ In some cases, full system wipe is the only reliable removal method
Step 6: Recover encrypted files
You have two options:
- Restore from clean backups (best method)
- Use ransomware decryption tools (limited availability)
➡ File recovery is not always guaranteed
Remove The Ransomware Virus: Understanding ransomware
Ransomware gets its name from the fact that it tries to trick or force a victim into paying money to solve a problem. Depending on the form of ransomware, the problem may be non-existent, in other words, it may be a pure trick, or it may be very serious. Here are the three main forms of ransomware and what to do about them.
Scareware
Scareware is pure trickery. All it does is place an intimidating message on the victim’s screen and hope that they will act on it. Its creators hope that if they target enough people, some of them will be intimidated into paying up. The reality is that all you need to do is install a reputable anti-malware program, have it scan your computer, and follow its instructions about what files need to be deleted.
Lockware is actually very similar to scareware. The only real difference is that this time there is an actual problem, albeit one which is very easy to solve with a bit of know-how. Lockware essentially freezes your computer so you’re unable to use it.
It can, however, generally be bypassed if you just boot into safe mode (with command prompt in Windows) and restore to an earlier point in time. Then install a reputable anti-malware program and have it scan your computer just to make sure that it’s completely free of ransomware (and anything else).
Remove The Ransomware Virus: Encryption ransomware
Depending on how well-prepared you are, encryption ransomware is either the least annoying form of ransomware there is or an absolute nightmare. As its name suggests, encryption ransomware encrypts some or all of the files on your hard drive or your cloud storage.
It may also encrypt files in any systems which are connected to it. For example, if you run automated data backups to a portable hard drive, local storage network, or the same cloud, then the encrypted files are likely just to be copied straight into that, possibly overwriting healthy ones in the process. This is known as the “ricochet effect”.
Getting rid of the initial infection is generally very straightforward. Normally all you need to do is install a reputable anti-malware program, have it scan your computer, and follow its instructions about what files need to be deleted. The problem is that this will not decrypt your files.
If you have a data backup, then all you have to do is waste a bit of your time restoring from it. If you don’t, then your options are to hope there is a decryption tool available, pay the ransom (with all that implies) or just accept the loss of your files.
Finding a decryption tool
If you don’t have a backup, you have nothing to lose by trying to find a decryption tool. First of all, you need to find a ransomware identifier. This will analyze the ransom note and the sample files which are usually sent with it (to prove the cyberattacker means what they say) and will take its best guess as to what form of ransomware was used in the attack.
Once you know this, you can then search for a decryption tool. There are a couple of points to remember here. First of all, even if you find one, it’s a good idea to hold off the victory celebrations until you’ve found out if it actually works.
One of the big problems with encryption ransomware is that, despite all the advice to the contrary, enough people pay the ransom to finance the continual development of established forms of encryption ransomware as well as the creation of new ones. This means that tools to combat it very quickly become obsolete.
Secondly, the growth of ransomware has, very ironically, led to a growth in “ransomware decryption” scams. You, therefore, need to be careful to avoid compounding the problem by falling victim to one of them too!
Prevention is massively better than cure
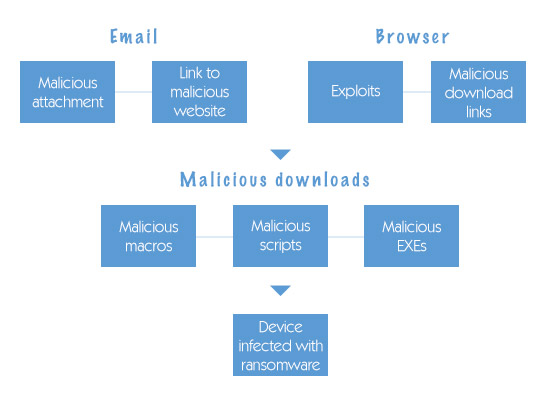
Possibly the most frustrating point about ransomware is that it really should be fairly straightforward to prevent it from attacking you in the first place. Invest in a robust anti-malware program with an integrated firewall and backed by a reputable brand and make sure that you always update your operating system and locally-installed software promptly.
Also, make sure you have a robust data backup process so that you can recover from any encryption ransomware which does get past your defenses.
Should You Pay the Ransom?
Never pay the ransom (recommended)
- No guarantee of file recovery
- Encourages future attacks
- May expose you to further exploitation
➡ Security experts strongly discourage paying attackers
Advanced ransomware response for businesses
- Disable compromised accounts and credentials
- Analyze network traffic for suspicious activity
- Block malicious IPs and domains
- Monitor for lateral movement across systems
- Engage incident response teams
➡ These steps help eliminate hidden threats and prevent reinfection
Removal vs Recovery
| Action | Purpose | Outcome |
|---|---|---|
| Malware Removal | Eliminate ransomware | Stops further damage |
| System Reset | Remove deep infections | Clean environment |
| Backup Restore | Recover files | Full recovery (if available) |
| Decryption Tools | Unlock files | Partial or limited recovery |
Prevent Ransomware After Removal
How to prevent ransomware attacks
- Install endpoint detection & response (EDR)
- Keep systems and software updated
- Enable automatic backups (offline + cloud)
- Use email and phishing protection
- Apply least-privilege access controls
➡ Prevention is the most effective long-term defense
Please click here now to start your free 30-day trial of Xcitium AEP.
Related Sources: