Forensic Analysis
Updated on October 21, 2022, by Xcitium
Updated on October 21, 2022, by Xcitium
Please give us a star rating based on your experience.

There are many possible problems you might encounter if you are using a Windows system. Either you s...
Ransomware Tools with ransomware constantly evolving, almost everyone can be at risk of advanced ran...
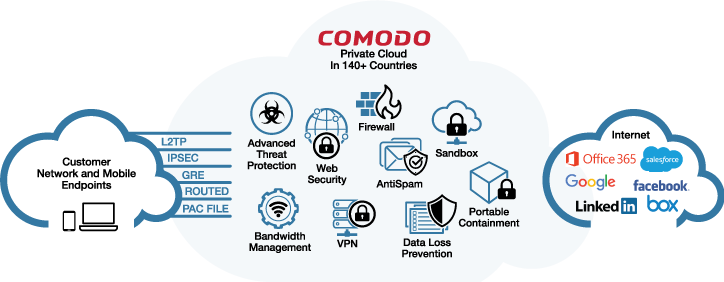
Cloud-Delivered Secure Web Platform Xcitium Dome is a revolutionary Cloud Delivered Secure Web Platf...

How is Ransomware defined and explained? The defining feature of ransomware is that it attempts to t...
The great amount of exposure to the computers and networks provides awareness to cyber threats such ...
Once malware infects your computer, it attacks the file system and targets valuable files. Before it...
Ransomware hitting the computer is devastating. This malware encrypts files and locks computer, rend...

Malware Virus is defined as a harmful application that pretends to be useful software. Malware virus...

Deal With Ransomware On Linux: Ransomware on Linux For years Ransomware on Linux, and its close rela...
Anti Malware: Malware Protection Malware protection is often mistaken as a simple security against m...
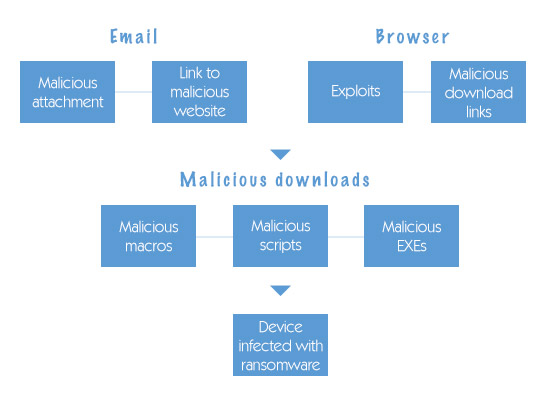
How Does Ransomware Get on your Computer? Ransomware is an advanced form of malicious malware that h...

Computer malware protection is a multi-layered defense against varieties of malware. It is an essent...